CSP Allow-list Experiment
Mirrored from Simon Willison for archival readability. Support the source by reading on the original site.
13th May 2026
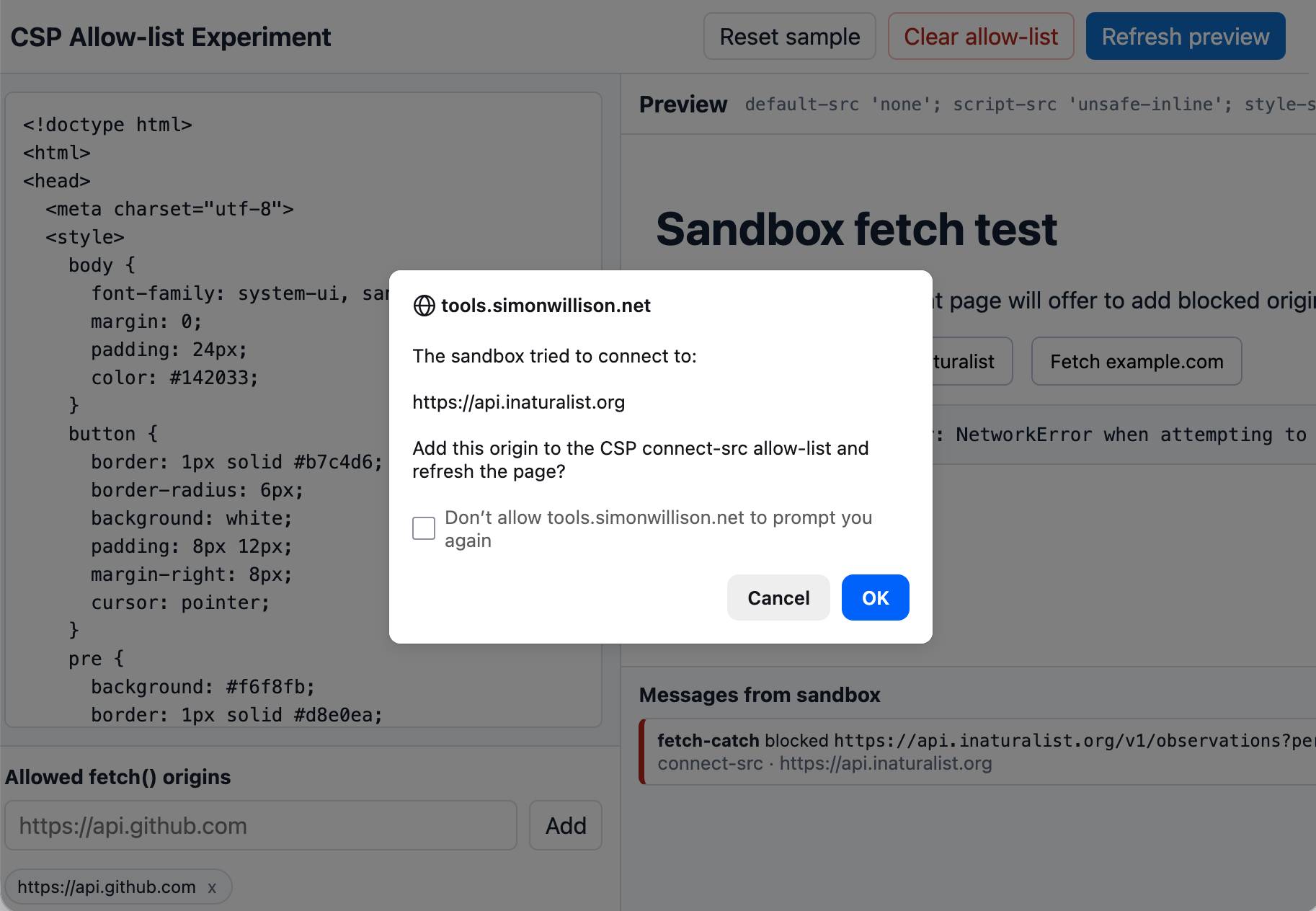
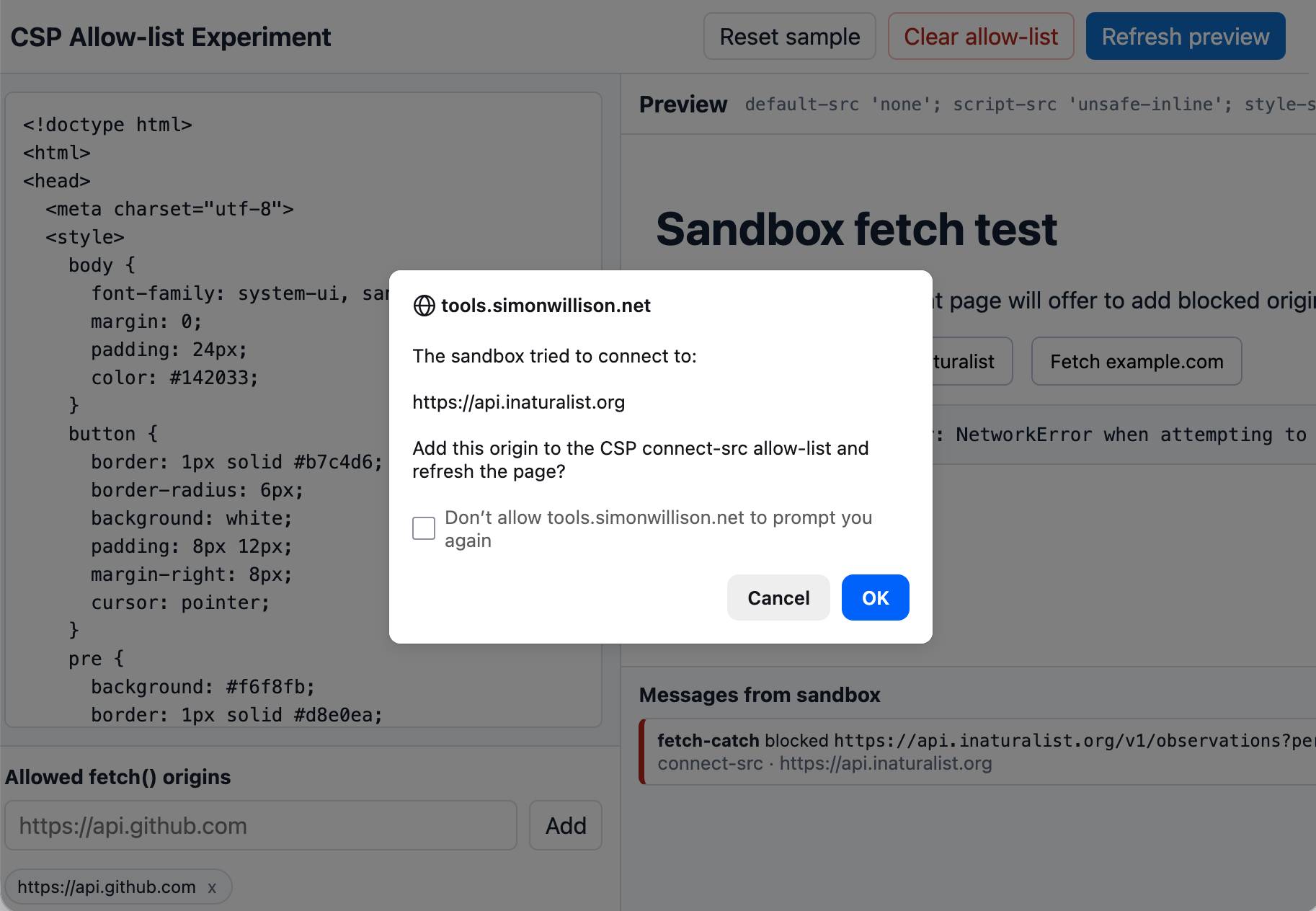
An experiment that shows that you can load an app in a CSP-protected sandboxed iframe (see previous note) and have a custom fetch() that intercepts CSP errors and passes them up to the parent window... which can then prompt the user to add that domain to an allow-list and then refresh the page.
I built this one with GPT-5.5 xhigh running in the Codex desktop app.
Posted 13th May 2026 at 4:50 am
Recent articles
- Notes on the xAI/Anthropic data center deal - 7th May 2026
- Live blog: Code w/ Claude 2026 - 6th May 2026
- Vibe coding and agentic engineering are getting closer than I'd like - 6th May 2026
This is a beat by Simon Willison, posted on 13th May 2026.
iframes 23 security 603 content-security-policy 11Monthly briefing
Sponsor me for $10/month and get a curated email digest of the month's most important LLM developments.
Pay me to send you less!
Discussion (0)
Sign in to join the discussion. Free account, 30 seconds — email code or GitHub.
Sign in →No comments yet. Sign in and be the first to say something.